Iso 27001 Description
What is ISO 27001?
1,855 Iso 27001 jobs available on Indeed.com. Apply to Quality Assurance Analyst, Help Desk Analyst, Risk Analyst and more! It may sound rather funny, but ISO 27001 does not require a company to nominate a Chief Information Security Officer, or any other person who would coordinate information security (e.g., Information security officer, Security manager, etc.).
ISO 27001 (formally known as ISO/IEC 27001:2005) is a specification for an information security management system (ISMS). An ISMS is a framework of policies and procedures that includes all legal, physical and technical controls involved in an organisation's information risk management processes.
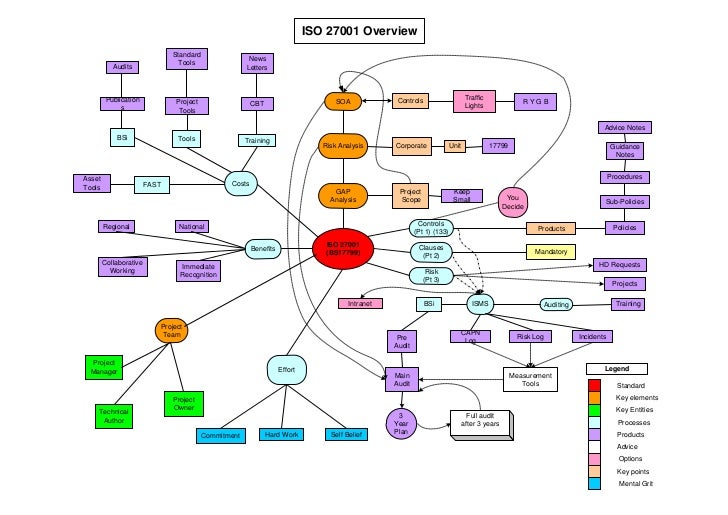
According to its documentation, ISO 27001 was developed to 'provide a model for establishing, implementing, operating, monitoring, reviewing, maintaining and improving an information security management system.'
ISO 27001 uses a topdown, risk-based approach and is technology-neutral. The specification defines a six-part planning process:
This is going to be the last one, we already saw the best value security camera system and the best security camera system for the money. Home video surveillance software. This is made for a big home or a small business, or both, this can actually might be the best security camera systems for small business, and we are going back to the.So here you have the, we are going to be really short on this one, because you already know the brand, so you know that it is really good.They bring you great quality, remote viewing, widescreen, access and compatibility with almost all devices, power on Ethernet, manual zoom, and 1 year of warranty. Also, you don’t need to handle a lot of cables for installation, this Wi-Fi technology is easy to handle for people who are not really friends with the wiring. We are going deeper every time we change brands, here is a new one from you have the Reolink Poe Home security camera system, best security camera systems for home maybe, it had great capacity of storage, quality is good and will record 24/7 if needed, you will receive alerts instantly every time it detects a treat, also it is really easy to set up.with every other Poe camera that you already have, so you don’t need to actually change our whole security system if you want to work with these ones. Next is a simple one, but that doesn’t mean that is not worth it, from the Zmodo brand, you have the, another wireless!Sometimes these could be the best buy surveillance camera system, this one is really easy to use and install, you will have 720p quality in each one, local and also remote monitoring.You also have a cloud service to store all of your footage always safe, 24/7 recording and professional customer support.
- Define a security policy.
- Define the scope of the ISMS.
- Conduct a risk assessment.
- Manage identified risks.
- Select control objectives and controls to be implemented.
- Prepare a statement of applicability.
The specification includes details for documentation, management responsibility, internal audits, continual improvement, and corrective and preventive action. The standard requires cooperation among all sections of an organisation.
The 27001 standard does not mandate specific information security controls, but it provides a checklist of controls that should be considered in the accompanying code of practice, ISO/IEC 27002:2005. This second standard describes a comprehensive set of information security control objectives and a set of generally accepted good practice security controls.
ISO 27002 contains 12 main sections:
Iso 27001 Definition Of Security Incident
1. Risk assessment
2. Security policy
3. Organization of information security
4. Asset management
5. Human resources security
6. Physical and environmental security
7. Communications and operations management
8. Access control
9. Information systems acquisition, development and maintenance
10. Information security incident management
11. Business continuity management
12. Compliance
Organisations are required to apply these controls appropriately in line with their specific risks. Third-party accredited certification is recommended for ISO 27001 conformance.
Other standards being developed in the 27000 family are:
Iso 27001 Description System
- 27003 – implementation guidance.
- 27004 - an information security management measurement standard suggesting metrics to help improve the effectiveness of an ISMS.
- 27005 – an information security risk management standard. (Published in 2008)
- 27006 - a guide to the certification or registration process for accredited ISMS certification or registration bodies. (Published in 2007)
- 27007 – ISMS auditing guideline.